 Despite UDP being ubiquitous on pretty much any other OpenVPN platform, for a long while Mikrotik only supported TCP variant. With Mikrotik RouterOS 7 finally being released earlier this year, we at last got an UDP support for OpenVPN.
Despite UDP being ubiquitous on pretty much any other OpenVPN platform, for a long while Mikrotik only supported TCP variant. With Mikrotik RouterOS 7 finally being released earlier this year, we at last got an UDP support for OpenVPN.
For some people UDP/TCP difference might not matter much. If you have a stable connection chances are you really don't need to care - OpenVPN via TCP will serve you without any issues.
But, if you are dealing with multiple connections over a high latency and/or lossy network, UDP will be much faster as lost packets for one connection will not impact the other. How big the difference is? Well, I have a connection between USA and Croatia and it leaks like a sieve. My speed went from about 400 Kbps to 1000 Kbps just due to this change (tested using 2 parallel connections). I would say switching to UDP was well worth the effort for my use case.
Getting UDP enabled for OpenVPN server once you get Mikrotik 7.1 or higher running is trivial assuming you have OpenVPN via TCP already configured. You just change Protocol value to udp, update your client side with the same change (albeit for proto field) and you're done.
But, in the interest of completeness, let's see how one would create such config from scratch.
First we create all the certificate templates (give it at least 10 years validity):
Certificate templates/certificate
add name=ca-template common-name=example.com days-valid=3650 \
key-size=2048 key-usage=crl-sign,key-cert-sign
add name=server-template common-name=*.example.com days-valid=3650 \
key-size=2048 key-usage=digital-signature,key-encipherment,tls-server
add name=client-template common-name=client.example.com days-valid=3650 \
key-size=2048 key-usage=tls-client
As far as OpenVPN server is concerned, you can use whatever you want for certificate's common name. Since some other VPNs are not as forgiving (yes SSTP, I am looking at you), I made it a habit to use either external IP or the host name here.
Once we have templates sorted out, we can do the signing:
Certificate signing/certificate
sign ca-template name=ca-certificate
sign server-template name=server-certificate ca=ca-certificate
sign client-template name=client-certificate ca=ca-certificate
And then exporting certificate material:
Certificate export/certificate
export-certificate ca-certificate export-passphrase=""
export-certificate client-certificate export-passphrase=12345678
This should give you three files: cert_export_ca-certificate.crt, cert_export_client-certificate.crt, and cert_export_client-certificate.key. After copying these files to the computer for later I like to rename them to ca.crt, client.crt, and client.key respectively. It just makes everything a bit tidier.
Next we need a separate pool of IP addresses for clients. I will assume you have your clients in some other network (e.g. 192.168.1.x) and this new network is just for VPN:
DHCP pool/ip
pool add name="vpn-pool" ranges=192.168.8.10-192.168.8.99
Instead of editing the default encrypted profile, we can create a new one. If you use different DNS server, do change it here, and while at it, you should really use a bit more imaginative user/password pair:
VPN profile/ppp
profile add name="vpn-profile" use-encryption=yes idle-timeout=10m \
local-address=192.168.8.250 dns-server=1.1.1.1 remote-address=vpn-pool \
secret add name=user profile=vpn-profile password=password
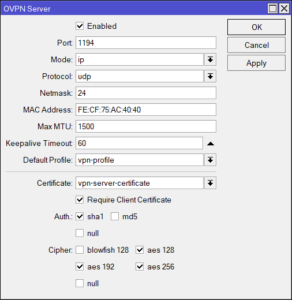
Finally, we can enable OpenVPN server interface:
OpenVPN server/interface ovpn-server server
set default-profile=vpn-profile certificate=server-certificate require-client-certificate=yes \
auth=sha1 cipher=aes128,aes192,aes256 enabled=yes protocol=udp
Assuming you're using Windows, you can copy both ca.crt and client.crt to C:\Program Files\OpenVPN\config\ directory alongside client.ovpn. On Linux, one would do the same, just in the /etc/openvpn/client directory.
You don't have client.ovpn? Well, one is in sample-config directory and we just need to change/add the highlighted items. And since we're finally using UDP, we can leave proto as it is.
clinet.ovpnclient
dev tun
proto udp
remote example.com 1194
resolv-retry infinite
nobind
persist-key
persist-tun
ca ca.crt
cert client.crt
key client.key
remote-cert-tls server
cipher AES-128-CBC
auth SHA1
auth-user-pass
redirect-gateway def1
verb 3
A bit annoying step is being asked for the private key passphrase (in the addition to the username/password pair). Mikrotik doesn't allow export without it but fortunately we can use OpenSSL to change that:
OpenSSL key adjustments> openssl.exe rsa -in client.key -out client.key
Enter pass phrase for client.key: 12345678
writing RSA key
With this, your VPN connection should work like a charm.
PS: Do not forget to adjust firewall if necessary (TCP port 1194).
Firewall/ip firewall filter
add chain=input protocol=udp dst-port=1194 action=accept place-before=0 comment="Allow OpenVPN"
Consider switching to wireguard! That’s a lot faster.
AVM I going to support this soon, a few others already do. There is a solution for a raspberry if needed.
I did consider it but frankly its not there yet for me. I am playing with Wireguard between two Mikrotik routers a few countries apart and NAT issues make it unworkable for me. I’m not sure if this is something Mikrotik-related or my personal setup though. Either way, I haven’t found fool-proof configuration for Wireguard on Mikrotik yet.
In my experience SSTP is actually protocol that causes the least amount of problems when it comes to traversing unfriendly networks as it gets detected as HTTPS most of the time. Albeit SSTP has it’s own issues…
Dear Josip,
thanks for your great post. My scenario is that I have working OpenVpn service on MT through TCP and for the throughput reason, I would like to change (try) it to UDP. And so far without success. I followed your tutorial, surfed, and tried almost every google hit and documentation without a working solution. In UDP setup my OpenVPN does not connect.
Would you be so kind and give me a hint about what would I need to try differently?
Many Thanks,
Samo
—
GCM:AES-128-GCM). Future OpenVPN version will ignore –cipher for cipher negotiations. Add ‘AES-256-CBC’ to –data-ciphers or change –cipher ‘AES-256-CBC’ to –data-ciphers-fallback ‘AES-256-CBC’ to silence this warning.
Wed Jan 12 23:33:35 2022 Flag ‘def1’ added to –redirect-gateway (iservice is in use)
Wed Jan 12 23:33:35 2022 OpenVPN 2.5.5 Windows-MSVC [SSL (OpenSSL)] [LZO] [LZ4] [PKCS11] [AEAD] built on Dec 15 2021
Wed Jan 12 23:33:35 2022 Windows version 10.0 (Windows 10 or greater) 64bit
Wed Jan 12 23:33:35 2022 library versions: OpenSSL 1.1.1l 24 Aug 2021, LZO 2.10
Wed Jan 12 23:33:35 2022 MANAGEMENT: TCP Socket listening on [AF_INET]127.0.0.1:25341
Wed Jan 12 23:33:35 2022 Need hold release from management interface, waiting…
Wed Jan 12 23:33:35 2022 MANAGEMENT: Client connected from [AF_INET]127.0.0.1:25341
Wed Jan 12 23:33:36 2022 MANAGEMENT: CMD ‘state on’
Wed Jan 12 23:33:36 2022 MANAGEMENT: CMD ‘log all on’
Wed Jan 12 23:33:36 2022 MANAGEMENT: CMD ‘echo all on’
Wed Jan 12 23:33:36 2022 MANAGEMENT: CMD ‘bytecount 5’
Wed Jan 12 23:33:36 2022 MANAGEMENT: CMD ‘hold off’
Wed Jan 12 23:33:36 2022 MANAGEMENT: CMD ‘hold release’
Wed Jan 12 23:33:41 2022 MANAGEMENT: CMD ‘password […]’
Wed Jan 12 23:33:41 2022 TCP/UDP: Preserving recently used remote address: [AF_INET]8x.1×9.x7.2×4:1194
Wed Jan 12 23:33:41 2022 Socket Buffers: R=[65536->65536] S=[65536->65536]
Wed Jan 12 23:33:41 2022 UDP link local: (not bound)
Wed Jan 12 23:33:41 2022 UDP link remote: [AF_INET]8x.1×9.x7.2×4:1194
Wed Jan 12 23:33:41 2022 MANAGEMENT: >STATE:1642026821,WAIT,,,,,,
Wed Jan 12 23:34:41 2022 TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity)
Wed Jan 12 23:34:41 2022 TLS Error: TLS handshake failed
—
client
—
client
dev tun
proto udp
remote x.y.z.w 1194
nobind
persist-key
persist-tun
tls-client
remote-cert-tls server
ca CA_Doma_Exprt.crt
cert CLI_Doma_Exprt.crt
key CLI_Doma_Exprt.key
verb 3
mute 10
cipher AES-256-CBC
auth SHA1
auth-user-pass secret
auth-nocache
redirect-gateway autolocal
—
Firewall I copied your command. Arp proxy on LAN Bridge.
Hard to say frankly. Based on your log, packets are simply not coming back. To me this smells as either firewall or routing issue. Since you have the same server serving TCP OpenVPN without issues, I would think firewall.
First thing I would try is to move filter higher up – it could be a deny above that’s blocking the packets.
We had same problem. For some reason UDP packets are getting lost causing TLS handshake failure or connection timeouts at random. We switched back to TCP. Btw, we have CCR2004-16G-2S+ router running 7.1.3 RouterOS. I bet it is a bug in RouterOS. We are now considering using IPSec VPN instead of OVPN. OVPN is a bit neglected by Mikrotik.
what client are using for windows?
thank you
Dear Josip, Roberto,
many thanks for your kind reply, sorry for my late reply.
I have Mikrotik OpenVPN (all on the same device), the client is indeed Windows (11). This same setup works like a charm with the TCP configuration. But it is kind of slow(ish).
I have two Synology servers to synchronize over the night so I would benefit from extra bandwidth that is why I consider at least test with the UDP.
My scenario:
– on mikrotik 7.1.1 , PPP; Interface, openvpn – change to UDP protokol (only change)
– on Mikrotik 7.1.1, IP, firewall, filter rules – change from TCP to UDP (Chain-input, protocol UDP 17, dstport 1194, action-accept
– /no NAT user configuration beside default masquerade/
– on windows client – change proto from TCP to UDP (the only change). The same behavior is on my iPhone on wifi and LTE (A1).
/- ISP does not block me in some way as I have my modem in Bridge /
Thank you, wish you all the best,
Samo
Hello,
as per my call to my ISP they enabled UDP (openvpn) traffic for my bridge and reboot – so it is finally working now!!! Thank you for your energy and good will, stay safe.
Br, Samo
bump.
Perhaps anyone found something new regarding the issue?
(I think I am suffering from the same symptoms:
everything works with TCP, but when just changing the protocol to UDP on both sides i get messages flooding the log on routeros 7.5, and tls timeout on the client)
Is it possible to have both UDP and TCP enabled for OpenVPN?
Unfortunately, it’s one or the other. Both TCP and UDP don’t work at the same time.
# Config OVPN v2.5
client
dev tun
proto udp
remote example.com 1194
route 192.168.1.0 255.255.255.0
cipher AES-256-CBC
data-ciphers AES-256-CBC
auth SHA1
resolv-retry infinite
nobind
persist-key
persist-tun
remote-cert-tls server
auth-user-pass
auth-nocache
verb 3
I know that there must be certificates in the file. I only provided config. As for the route, it must be entered, because if I do not enter it, I have access to devices in the local network, but I do not have the Internet.
I know that there must be certificates in the file. I only provided config. As for the route, it must be entered, because if I do not enter it, I have access to devices in the local network, but I do not have the Internet.
But you need to add certificates to the koinfig file or like external files. Set the route under the remote network. OVPN 2.5 doesn’t crash any bugs.
Hi Medo,
is it possible to have just one .ovpn file with all information in it so that I can use it in thirdparty apps?
It`s possible when I have freeovpn server on ubuntu but with mikrotik I haven`t had luck..
Thanks,
Matija
Do you have an idea how to use Shared Key instead of TLS?
Can you explain better about certificate creation. I do not understand how to get the .key file as stated above. I only get the .crl files.
Sorry, I accidentally removed step that exports key after signing. Added it back in.
Hi, I followed your guide, but I am not able to set up the vpn from my Windows10 PC. After I have entered the Private Key Passphrase I get an error “read UDP: Unknown error (code=10054)”.
I paused my firewall protection in the PC, but the fault remains.
In the Mikrotik server is in the firewall a rule: chain=input action=accept protocol=udp dst-port=1194 log=yes log-prefix=”openvpn”. There are no drop rules with a lower line number.
This my log:
2023-04-19 16:58:56 Restart pause, 5 second(s)
2023-04-19 16:59:01 TCP/UDP: Preserving recently used remote address: [AF_INET]x.x.x.x:1194
2023-04-19 16:59:01 Socket Buffers: R=[65536->65536] S=[65536->65536]
2023-04-19 16:59:01 UDP link local: (not bound)
2023-04-19 16:59:01 UDP link remote: [AF_INET]x.x.x.x:1194
2023-04-19 16:59:01 MANAGEMENT: >STATE:1681916341,WAIT,,,,,,
2023-04-19 16:59:01 read UDP: Unknown error (code=10054)
2023-04-19 16:59:03 read UDP: Unknown error (code=10054)
2023-04-19 16:59:07 read UDP: Unknown error (code=10054)
2023-04-19 16:59:15 read UDP: Unknown error (code=10054)
2023-04-19 16:59:31 read UDP: Unknown error (code=10054)
2023-04-19 17:00:01 TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity)
2023-04-19 17:00:01 TLS Error: TLS handshake failed
2023-04-19 17:00:01 SIGUSR1[soft,tls-error] received, process restarting
2023-04-19 17:00:01 MANAGEMENT: >STATE:1681916401,RECONNECTING,tls-error,,,,,
2023-04-19 17:00:01 Restart pause, 5 second(s)
2023-04-19 17:00:06 SIGTERM[hard,init_instance] received, process exiting
2023-04-19 17:00:06 MANAGEMENT: >STATE:1681916406,EXITING,init_instance,,,,,
—————————————————
And this is my config:
# Configuration for Windows OpenVPN client
# use char ; to comment line
client
dev tun
# We can replace TCP with UDP since Mikrotik RouterOS version 7.1
proto udp
remote x.x.x.x 1194
resolv-retry infinite
nobind
persist-key
persist-tun
# Copy files to C:\Program Files\OpenVPN\config.
ca myCa_Mariadonk.crt
cert clientLT.crt
key clientLT.key
remote-cert-tls server
cipher AES-128-CBC
# We must use data-ciphers otherwise we get TLS key negotiation failed – TLS handshake failed from Mikrotik
data-ciphers AES-128-CBC
auth SHA512
# User authentication
# provide credentials for user in secret.cfg
auth-user-pass
;auth-user-pass secret.cfg
# Push a default route to a client so Internet traffic flows via Mikrotik
redirect-gateway def1
# Add route to reach PC on primary subnet 192.168.88.0/24. This is required only when we do not push a default route with “redirect-gateway def1”
;route 192.168.88.0 255.255.255.0 192.168.100.1
verb 3
auth-nocache
—————————————————
Do you have any suggestions?
Hi, thanks for the guide, it works perfectly! a question, if I wanted a split tunnel what should I do? I would like to avoid internet traffic on the VPN… Thanks