 When I published post about OpenVPN on CentOS most common comment was "How to do that on some more user-friendly distribution. Well, you don't get much more friendlier than Mint 16 (Petra).
When I published post about OpenVPN on CentOS most common comment was "How to do that on some more user-friendly distribution. Well, you don't get much more friendlier than Mint 16 (Petra).
Before starting with anything we need to install OpenVPN package. This is done via Menu, Administration, Software Manager. Just type OpenVPN and install first thing you get back (yep, this is great piece of security advice ;)).
First we can do the easy stuff. Download PIA's OpenVPN configuration files and extract it to directory of your choice. I kept them in /home/MyUserName/pia.
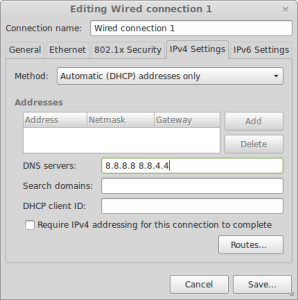
Next easy step is setting up DNS resolving. For that we go to Menu, Preferences, Network Connections. Just click edit on connection you are using and go to IPv4 Settings tab. Change Method to Automatic (DHCP addresses only). Under DNS servers enter 209.222.18.222 209.222.18.218 (PIA's DNS).
All other commands are to be executed in terminal and most of them require root privileges. It might be best if you just become root for a while:
$ su - rootNext step is getting configuration in place (replace username and password with yours):
# cp /home/MyUserName/pia/ca.crt /etc/openvpn/ca.crt
# cp /home/MyUserName/pia/crl.pem /etc/openvpn/crl.pem
# cp /home/MyUserName/pia/US\ Midwest.ovpn /etc/openvpn/client.conf
# sed -i "s*ca ca.crt*ca /etc/openvpn/ca.crt*" /etc/openvpn/client.conf
# sed -i "s*crl-verify crl.pem*crl-verify /etc/openvpn/crl.pem*" /etc/openvpn/client.conf
# echo "auth-user-pass /etc/openvpn/login.pia" >> /etc/openvpn/client.conf
# echo "mssfix 1400" >> /etc/openvpn/client.conf
# echo "username" > /etc/openvpn/login.pia
# echo "password" >> /etc/openvpn/login.pia
# chmod 500 /etc/openvpn/login.piaNow we can test our connection (after we restart network in order to activate DNS changes):
# /etc/init.d/networking restart
# openvpn --config /etc/openvpn/client.confAssuming that this last step ended with Initialization Sequence Completed, we just need to verify whether this connection is actually used.
I found whatismyipaddress.com quite helpful here. If you see some mid-west town on map, you are golden (assuming that you don't actually live in US mid-west :)).
Now you can stop test connection via Ctrl+C in order to properly start it. In addition, you can specify it should start on each system startup:
# service openvpn start
# echo "AUTOSTART=all" >> /etc/default/openvpnLastly you can think about firewall and disabling default interface when VPN is not active. Of course, in order for things to work, we still need to allow port 1194 toward our VPN server and DNS:
# ufw default deny incoming
# ufw default deny outgoing
# ufw allow out on tun0
# ufw allow out 1194/udp
# ufw allow out on eth0 to 209.222.18.222 port 53 proto udp
# ufw allow out on eth0 to 209.222.18.218 port 53 proto udp
# ufw enableAnd that is all.
PS: It is not a déjà vu, article is really close to how it was set on CentOS.
[2016-10-01: Removed auth-nocache directive as it didn't play nice with auth-user-pass.]
This is basically perma-vpn. How would one turn this off, or reverse it.
Just do
service openvpn stop
followed by
service networking restart
I got
~ $ service openvpn stop
* Stopping virtual private network daemon(s)…
* Stopping VPN ‘client’
/etc/init.d/openvpn: 102: kill: Operation not permitted
rm: cannot remove ‘/var/run/openvpn.client.pid’: Permission denied
I’m an idiot, just needed root.
Thanks for the help!
After running: sudo openvpn –config /etc/openvpn/client.conf
I get this:
Options error: You must define TUN/TAP device (–dev)
Use –help for more information.
Suggestions?
n/m. Forgot to run this line here:
cp /home/MyUserName/pia/US\ Midwest.ovpn /etc/openvpn/client.conf
because I had downloaded the openvipn.zip directly to /etc/openvpn. Derpderp.
After I run “openvpn –config /etc/openvpn/client.conf”
I get…
“Options error: –ca fails with ‘ca.crt’: No such file or directory
Options error: Please correct these errors.
Use –help for more information.”
I did use “East” instead of “Midwest” in “cp /home/MyUserName/pia/US\ Midwest.ovpn /etc/openvpn/client.conf”… But i don’t see why that would be a problem?
Any help would be muchhh appreciated :)
Sorry if the anwser’s obvious, today’s only my second day with linux…
It looks as if ca.crt file is not in /etc/openvpn/ directory.
Did you run
cp /home/MyUserName/pia/ca.crt /etc/openvpn/ca.crt
(do replace “MyUserName” for user name and “pia” for directory where you extracted PIA’s OpenVPN files)?
ya I did, when I run “ls /etc/openvpn/” it shows “ca.crt client.conf login.pia update-resolv-conf” but i still get the same message?
I also retried it with midweast instead of east with no luck either.
It seems that there are few things slightly different in client.conf compared to when I downloaded it last time. These steps were missing:
cp /home/MyUserName/pia/crl.pem /etc/openvpn/crl.pem
sed -i “s*ca ca.crt*ca /etc/openvpn/ca.crt*” /etc/openvpn/client.conf
sed -i “s*crl-verify crl.pem*crl-verify /etc/openvpn/crl.pem*” /etc/openvpn/client.conf
This is a super old post, but it worked perfectly to get me going.
What I wonder is, if I want to switch to the UK or Sweden or wherever, do I just go back into root and re-do cp /home/MyUserName/pia/US\ Midwest.ovpn /etc/openvpn/client.conf but swap out the .ovpn file?
Also – are you aware of any way to make a kill switch through cli? I can set it up in my router but I’d prefer to just do it all on the computer. Thank you!
Just copy other .ovpn file and you’re golden.
The way I setup this, you don’t need kill switch. If VPN breaks you lose your connection completely…